Anatomy of a Linux Ransomware Attack
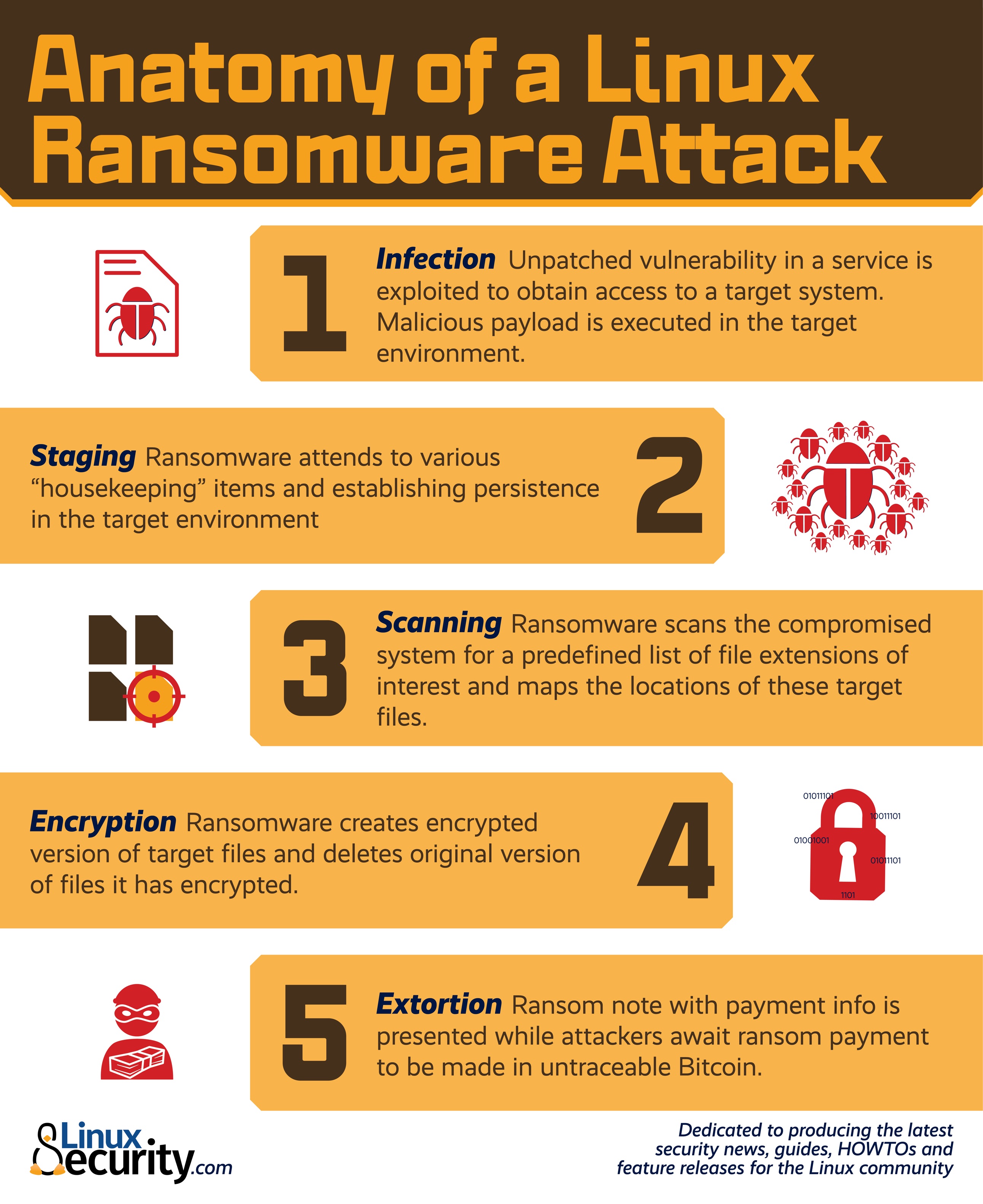
Here are our top tips and advice for protecting against Linux Ransomware:
Backup critical files and diversify the storage media to avoid a single point of failure (SPOF). This won’t prevent an attack, but can mitigate potential damage.
Keep servers and endpoints up to date to ensure that they use the latest security patches.
Implement the principle of least privilege for user accounts.
Monitor network activity and system logs closely.
Keep tabs on event logs to identify anomalous behavior before it causes harm.
Use a combination of IP filtering, an intrusion detection system (IDS) and an intrusion prevention system (IPS).
Use Linux security extensions that control and restrict access to data or network resources.
Implement robust network segmentation and data compartmentalization to minimize the impact of a potential ransomware attack.
Audit systems regularly.
More on: https://linuxsecurity.com/features/anatomy-of-a-linux-ransomware-attack
4MLinux
AaricKDE Linux
Abyss Web Server
Accessible-Coconut Linux
ACIAH Linux
Adelie Linux
Adobe
AETHEROS Linux
AgarimOS Linux
AI
airyxOS BSD
Alchg Linux
Alfheim Linux
Alien-OS Linux
AllegianceOS Linux
AlmaLinux
Alter Linux
Amoeba Linux
AmogOS Linux
AmOs Linux
Anadolu Panteri Linux
AndEX Linux
Android
Android Applications
Android Software
Antivirus
Antivirus Live CD Linux
AOS Linux
Apache Web Server
API
Apple
Apple Time Machine Backup Server
Apple Watch
Arch Hurd Linux
Arch Linux
Archcraft Linux
ArchEX Linux
Armbian Linux
Artificial Intelligence
Asahi Linux
AshOS Linux
Asril OS Linux
astOS Linux
Astra Linux
Astronomy Linux
Ataraxia Linux
Athena OS Linux
AUSTRUMI Linux
Auxtral Linux
AVMultimedia Linux
Avouch Linux
AxOS Linux
AzzeraOS Linux
Bash
Basic Linux
Bentoo Linux
Big Brother
Bing
Birds Linux
Bitrig BSD
Black Axe Gang
BlackWeb Linux
blendOS Linux
Bliss OS Linux
BlissRoms Linux
blueflops Linux
Bottlerocket Linux
Br OS Linux
BrazilFW Linux
BSD
BSD Distros
BSD Security
Bugs
Business-OS Linux
CachyOS Linux
CalinixOS Linux
carbonOS Linux
Carbs Linux
CasaOS Linux
CDlinux
Cereus Linux
Chimera Linux
ChimeraOS Linux
China
Chrome
ChromeOS Flex Linux
Chromium
Circle Linux
Clandestine Agencies
Clandestine Operations
CLI
Closed Source Linux Distros
Closed Source Software
Cloud
Cloud VM
CloudLinux OS
CloudNeedle OS Linux
CloverOS Linux
Collapse OS Linux
Command Line
Command Not Found
Communism
Communist Fascism
Computer
Computer Freedom
Computer Fun
Computer History
Computer Humor
Computer Jokes
Computer Memes
Computer Operating Systems
Computer Programming
Computer Security
Computer Users Rights
Computing
Condres OS Linux
Consumers Rights
Cookies
Copilot
Corporatism
Coyote Linux
CROWZ Linux
Crunchbang++ Linux
CryptoCurrency OS Linux
Crystal Linux
Cubuntu Linux
Cucumber Linux
Cyber Crime
Cyber Fraud
Cyber Mafia
Cyclone OS Linux
dahliaOS Linux
Damn Small Linux
Damon Imani
DarkMAX
DarkOs Linux
DAT Linux
DBAN Linux
Debian
Debian 11
Debian GNU/Hurd Linux
DECODE OS Linux
Delicate Linux
Delinux
Desktop Environtments
Developers
Development
DFLinux
Digital Security
distri Linux
Distro Hopping
Distrobox
DistroWatch
Dockers
Dog Linux
Donau Linux
Downloads
Dowse Linux
DragonOS Linux
Drauger OS Linux
DRBL Linux
Droidian Linux
Dusk OS Linux
eBPF
EdUBudgie Linux
EducaAndOS Linux
Educatux Linux
Electron
ELinOS Linux
eLux Linux
Emperor-OS Linux
Emulation
EmuTOS
Enchantment OS Linux
Eole Linux
EQuilibrium Linux
Escuelas Linux
EterTICs Linux
EU Legislation
EVA1 Linux
Exergos-Red Linux
Exodia OS Linux
Expirion Linux
eXtern OS Linux
Exton|OS Linux
EzShare Public Cloud Server
Facebook Fun
Facebook Humor
Facebook Jokes
Facebook Memes
Fedora Silverblue Linux
Fenix Linux
Fienix Linux
Filen
Firefox
Flatcar Container Linux
fli4l Linux
Floppix Linux
floppyfw Linux
FluXuan Linux
FontOnLake Malware
Fopnu
Forge OS Linux
FOSS
Free Open Source Software
FreedomOS Linux
Freeduc Linux
FreeRTOS
Freesco Linux
Fun
FX64 Linux
gabeeOS Linux
GalliumOS Linux
GALPon Linux
GDPR
German Government
Get-Free-OS Linux
GitHub
Gnome
Gnome Foundation
GNU
GNU Hurd Linux
GNU Linux-libre
Gnuinos Linux
GNUSTEP Linux
GobMis Linux
Good Life Linux
gorizont-rtlsdr Linux
GPL
Graphical User Interface
GUI
Hack
Hackers
Hacking
Hannah Montana Linux
Hardware
Hardware Development
HasCodingOS Linux
heads Linux
HefftorLinux
helloSystem BSD
Hive Ransomware
Hos OS Linux
Huayra Linux
Human Rights
Humor
HyperBian Linux
Hyprland
IBM
iBuntu Linux
iLinux OS
iLinux OS File Server
iLinux OS IRP
iLinux OS System Server
iMedia Linux
Influencers
Ink Cartridges
instantOS Linux
Intel
Internet
Internet Crime
Internet Freedom
Internet Mafia
Internet Resources
Internet Security
ISO
JarroNegro Linux
JingOS Linux
Joborun Linux
JostroOS Linux
JuNest Linux
justbuntu Linux
K8S
Kaisen Linux
Kamarada Linux
KaNaPi Linux
KDE
Klaus Schawb
Knowledge Base
Kumuda OS Linux
Law Enforcement
Legacy OS Linux
Legal Issues
Letux-OS Linux
LibraZiK Linux
libreCMC Linux
Lightning Linux
LiGurOS Linux
Lilidog Linux
LineageOS Linux
Linkat Linux
Linux
Linux Applications
Linux Community
Linux Developers
Linux Development
Linux Distro Hopping
Linux Distros
Linux Distros Reviews
Linux Educacional
Linux Fun
Linux Funding
Linux Humor
Linux Jokes
Linux Kernel
Linux Lite
Linux Mafia Army
Linux Malware
Linux Memes
Linux OMG !
Linux Programming
Linux Ransomeware
Linux Reviews
Linux Security
Linux Software
Linux Tutorials
Linux Wallpapers
Linux Websites
LinuxBBQ
LinuxCNC
Lion Linux
Liri Linux
Liya Linux
LMSFM Linux
Loc-OS Linux
LOL
LuxOS Linux
LxPup Linux
Mac
MacintoshPi Linux
macOS
macOS Big Sur
Maemo Leste Linux
Mafia
MagOS Linux
Malware
Maqueta Abalar Libre Linux
MariaDB SQL Server
Mark Zuckerberg
Martine OS Linux
Mass Media
MassOS Linux
MathLibre Linux
Matrix
Maui Linux
Maui Project
Mazon OS Linux
Mbed Linux
mCOLe Linux
Memes
MenuetOS Linux
Meta
MetaCompany
Metis Linux
Metztli Reiser Linux
MeWe
Microsoft
Microsoft AI
mini-mimo Linux
Minimal Linux
MinIO Linux
MiniOS Linux
MINIX
MINIX 3 Linux
MIRACLE Linux
Miyo Linux
Mobian Linux
MocaccinoOS Linux
MODICIA O.S. Linux
MontaVista Linux
MorphOS Linux
Mozilla
MyNAS Linux
Nanolinux
Nard Linux
NayuOS Linux
Nazi Fascism
Nazism
Nelum-Dev1 Linux
NEMS Linux
Nerdy Daemon OS Linux
Neurolinux
New Entries
New Linux Websites
New Products
New Technologies
New World Order
Nigerian Mafia
Nitrux Linux
Nobara Linux
NodeOS Linux
NSA
NuttX Linux
NVIDIA
NVIDIA Cumulus Linux
oasis Linux
Obscurix Linux
OGOS Linux
OMG!
OmniOS Linux
Onix OS
Online Payments
Open Network Linux
Open Source Hardware
Open Source Linux Distros
Open Source Software
OpenCola
openEuler Linux
OpenStage Linux
openSUSE Linux
openSUSE MicroOS Linux
Openwall Linux
OpenWrt Linux
Opinions
Orange Pi OS Linux
Orchid Linux
Organized Crime
OS108 BSD
P2P
Parch Linux
Patriot OS Linux
Paywall
Peach OSI Linux
pearOS Linux
Pegasus OS Linux
Peropesis Linux
Personal Data
Peux OS Linux
Phoenix OS Linux
piCorePlayer Linux
Piracy
Pixel Linux
PlagueOS Linux
Plan 9 Unix
Plop Linux
PluriOS Linux
Pocket Linux
Politics
PorteuX Linux
POS OS Linux
postmarketOS Linux
Potabi Linux
Predator OS Linux
PrimeOS Linux
Printing
Privacy
Programming
Programming Languages
Propaganda
Proprietary Linux Distros
Proprietary Software
PsychOS Linux
Pyabr OS Linux
Python
Qlustar Linux
Quark OS Linux
Ransomware
Raspberry Pi
Raspberry Pi 5
RaspEX Linux
ravynOS BSD
Redox OS Unix
RedSleeve Linux
RefreshOS Linux
Regata OS Linux
Regolith Linux
Releax OS Linux
RELIANOID Linux
Reporters
Resilient Linux
RetroPie Linux
Rhino Linux
Richard Stallman
rlxOS Linux
Rocket Show Linux
Rocky Linux
Rolling Rhino Linux
RONIN Linux
RoshanOS Linux
Ryanboot Linux Netbooter
Sailfish OS
Salix Linux
Science Fiction
Sculpt OS Linux
Search Engines
Security
Security Onion Linux
SereneLinux
Servers
ShredOS Linux
SlimLinux
Slint Linux
snakeware Linux
SnowflakeOS Linux
Social Engineering
Social Networks
Software
Sovereign Tech Fund
SpaceFun Linux
Spark Linux
SpinelOS Linux
SpiralLinux
Split linux
SPRIND Federal Agency for Disruptive Innovation
stal/IX Linux
Star Wars
Startups
Static Linux
Steve Jobs
StormFish OS Linux
StormOS Linux
Stormtroopers
Sudo
SulinOS Linux
Super Simple Server
SUSE
SUSE Studio Express
Swap
SysLinuxOS
Talos Linux
TAZ Linux
Tech Industry
Technofascism
Technology
TeLOS Linux
TENS Linux
Terminal
ThomOS Linux
Time Machine Server Pro Linux
TinyOS Linux
TinyPaw Linux
Titan Linux
Tixati
Tizen Linux
tomsrtbt Linux
ToriOS Linux
Tribblix Linux
TROMjaro Linux
Tsurugi Linux
TTOS Linux
ttylinux
Tux Linux
TUXEDO OS Linux
Twister OS Linux
TxikiLinux
ubermix Linux
Ubuntu
Ubuntu 23.04 Lunar Lobster
Ubuntu Core Linux
Ubuntu Mini ISO Linux
Ubuntu Pro Linux
Ubuntu Sucks
Ubuntu Sway Remix Linux
Ubuntu Unity Linux
UbuntuDDE Linux
uCLinux
Ultramarine Linux
Unidockynapse CaleucheOS Linux
Unity
Unix
Unix Distros
Unraid OS Linux
Uplos32 Linux
USB
Utopia Linux
Vanilla Dpup Linux
Vanilla OS Linux
Vendefoul Wolf Linux
Venom Linux
Ventoy
Virage Linux
Virtual Memory
VirtualBox
Virus
Voyage Linux
Vuu-do Linux
Wake up!
wattOS Linux
Wayland
Wayland Compositors
Web Apps
Web Browsers
Web3
Websites
WEF
Windows
Windows 10
Windows 11
Windows 7
Windows 8
Windows 95
Windows Fun
Windows Humor
Windows Jokes
Windows Memes
Windows Samba File Sharing Server
Windows Updates
Windows XP
World Economic Forum
WTF!
Wxubuntu Linux
Xebian Linux
Xelph Linux
Xenia Linux
XeroLinux
Xiaopan OS Linux
Xinutop Linux
XOS Workstation Linux
YouTube
yt-dl
ytdl
ZealOS Linux
Zephix Linux
Zinc Linux
December 2023
November 2023
October 2023
September 2023
August 2023
May 2023
April 2023
March 2023
February 2023
January 2023
December 2022
November 2022
October 2022
September 2022
August 2022
July 2022
June 2022
May 2022
April 2022
March 2022
February 2022
January 2022
December 2021
November 2021
October 2021
September 2021

